Superior Managed IT Services in Wilmington, Delaware
With technology becoming an integral part of modern business operations, managing your IT infrastructure can be challenging. However, you can navigate this complex landscape with help. Partners Plus, your trusted Managed IT Services provider in Wilmington, Delaware, is here to assist!
The Partners Plus Advantage
At Partners Plus, we offer comprehensive IT services to businesses of all sizes and across multiple industries. Our services range from proactive IT support and security to cloud computing solutions, data backup, and recovery. We ensure your technology infrastructure is robust and helps you meet your business goals.
Managed IT Services – What We Offer
We provide a comprehensive Managed IT Services suite tailored to your unique business needs. Here’s what you can expect when you choose Partners Plus as your IT partner in Wilmington:
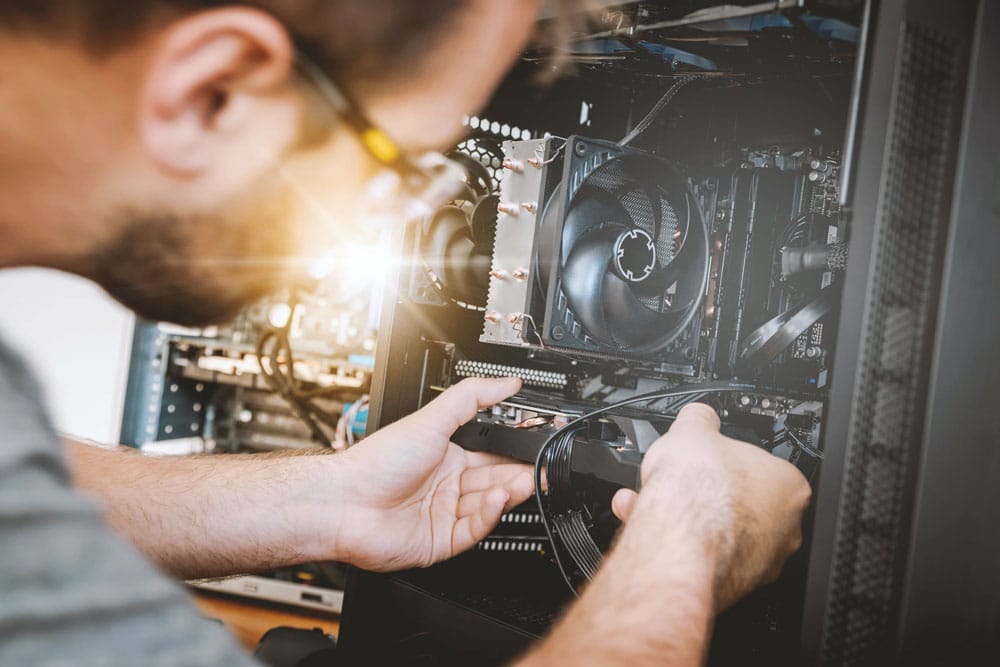
Proactive IT Support
We understand the importance of minimizing downtime and ensuring seamless operations. Hence, our IT support is proactive, preventing IT issues before they arise. Our team monitors your IT infrastructure 24/7 to detect and resolve problems promptly.
Robust IT Security
Securing your business data is our top priority. We implement advanced IT security measures, including antivirus solutions, firewalls, and intrusion detection systems. We also conduct regular security audits and compliance checks to identify and mitigate potential vulnerabilities.
Efficient Cloud Computing Solutions
Adopt the best of cloud technology with our cloud computing solutions. From assisting with cloud migration to providing ongoing support, we ensure your business benefits optimally from cloud services.
Reliable Data Backup and Recovery
Our data backup and recovery solutions are designed to safeguard your critical business data. We set up automated data backup processes and develop efficient recovery plans to protect your business from data loss scenarios.
Industry-Leading Managed IT Services in Wilmington
At Partners Plus, we are committed to delivering excellent IT services that make a difference. We understand that technology is a vital part of your business, and we strive to make it an asset for you, not a liability.
Why Choose Partners Plus?
Choosing Partners Plus for Managed IT Services in Wilmington means selecting a partner invested in your success. Our mission is to understand your business and its IT requirements thoroughly. This approach allows us to deliver solutions that align with your goals and budget.
Let’s Transform Your IT Together
Experience the difference between professionally Managed IT Services with Partners Plus. Contact us today to learn more about how our IT solutions can help drive your business forward. It’s time to leverage technology to its full potential – and we’re here to make that happen.
Wilmington, DE Managed IT Services
Partners Plus began in 1991 as an outsourced IT department after working as the Director of Programming and a Consultant for six years. For 30+ years now, we have been 100% committed to making sure small- and medium-sized business owners have the most reliable and professional virtual CIO in the Delaware Valley. Our dedicated team of professionals will solve your IT nightmares quickly and without confusion on your part.
Our customer-specific memberships deliver what you want and need without overstepping the boundaries of your budget. From cloud services and data backups to ransomware prevention and Dark Web monitoring, Partners Plus is here to work with you and your company for expert, dependable outsourced IT support and security in Wilmington.


Partners Plus
2 Penns Way, Suite 307
New Castle, DE 19720
Phone: 302-529-3700
Bill is an IT genius! He and his team are very efficient in working through our IT challenges.
We have worked with Partners Plus for the past four/five years. Quite simply, we wouldn’t stay with an outside vendor if they weren’t providing the service and results we require to do our work. I have never hesitated to give them a call to help us resolve our IT issues.
My experience working with Partners Plus is always pleasant and they usually exceed my expectations.
As the office manager for [a] CPA, I must say Partners Plus is a great IT company. Bill Hogan and [the] staff are always accessible – and in my office, especially during tax season, it is an absolute necessity! We have been with Partners for MANY years and they have seen us through our many hardware/software issues and changes with honesty, integrity, courtesy, and great service.
Our [auto group] has been a client for four years and our current in-house IT person [had] just retired… Bill and his crew stepped up their game and personally helped us by coming here weekly. Their professionalism, knowledge, and friendly staff make it very easy to get through some of our most difficult problems.
We moved our mid-sized firm to Partners Plus Inc and have been extremely pleased with the level of commitment, dedication, and security we have experienced since doing so. Bill and his team are always responsive, and thorough in explaining any questions we have, and are very knowledgeable and personable. In short, we could not ask for a better IT firm than Partners Plus Inc. We thought we were secure, but now we KNOW that we are.
About Wilmington, DE
Wilmington (Lenape: Paxahakink / Pakehakink) is the largest city in the U.S. State of Delaware. The city was built on the site of Fort Christina, the first Swedish settlement in North America. It lies at the confluence of the Christina River and Brandywine River, near where the Christina flows into the Delaware River. It is the county seat of New Castle County and one of the major cities in the Delaware Valley metropolitan area. Wilmington was named by Proprietor Thomas Penn after his friend Spencer Compton, Earl of Wilmington, who was prime minister during the reign of George II of Great Britain. As of the 2020 United States Census, the city’s population was 70,898. The Wilmington Metropolitan Division, comprising New Castle County, Delaware, Cecil County, Maryland, and Salem County, New Jersey, had an estimated 2016 population of 719,887. The Delaware Valley metropolitan area, which includes the cities of Philadelphia, Pennsylvania, and Camden, New Jersey, had a 2016 population of 6,070,500, and a combined statistical area of 7,179,357.
- Population (approx.): 72,000
- Geo coordinates: 39.7447°N, 75.5484°W
- Postcodes: 19801, 19899, 19898, 19885, 19895, 19884, 19893, 19894, 19886, 19802